Have you ever needed to add certificates to Key Vault parameters in D365FO and then clicked the Validate button just to have this obscure message pop up?
Did you then start wondering why the certificate couldn’t be found, just to find out that the secret identifier for the certificate needs to be in a specific format after searching for an answer on the net?
What about having to log onto the Azure portal just to check the expiration date of the certificate, because it still passes validation, even though it is expired?
How about other scenarios that aren’t checked by the standard validation?
Well, we’ve been wondering the same things while creating our Electronic signature certificates for signing documents (which you can check out here).
So we have decided to create a new validation feature with improved messaging to make it more evident what is wrong with a certificate or secret!
Best of all? It’s included in Docentric Free Edition starting with version 3.4.5!
Validation of the format of the secret identifier
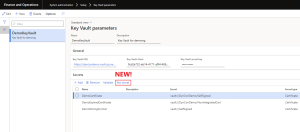
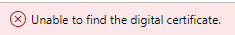
When adding a new certificate in the Key Vault parameters form, if the secret identifier is in the wrong format, the standard validation only checks if it starts with “vault://” and gives a generic error:
But with Docentric validation the message is now clear:
Validation of expired certificates
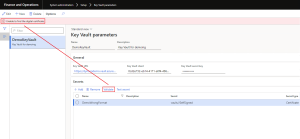
Now that we know what the correct format is, we add another certificate and press the standard Validate button again, to see if it is valid:
The validation is successful! This means that the certificate is ready to be used, right? Let’s check out the key vault on the Azure portal:
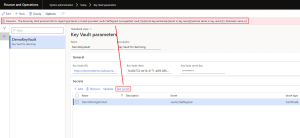
Looks like the certificate is expired! That’s no good at all, and even worse we had no idea without double checking.
Let’s try the Docentric validation:
Much better, now we know that the certificate needs to be renewed without having to check externally.
Validation of other scenarios
We’ve discussed the two most common scenarios that one would face whilst configuring certificates in Key Vault parameters.
But Docentric validation doesn’t just stop there, we’ve also added checks for several other scenarios, such as:
- If a certificate is issued in the future.
- If a certificate was revoked (checking the Certificate Revocation List (CRL)).
- If a certificate was tampered with.
- If a certificate has an invalid signature.
- If a certificate has an incomplete certificate chain (all the issuer certificates).
- If the certificate issuers were tampered with.

 Tags: Azure Key Vault, Certificates, D365FO, Free Edition
Tags: Azure Key Vault, Certificates, D365FO, Free Edition